[ad_1]

Getty Images
A newly discovered cryptomining worm is stepping up its targeting of Windows and Linux devices with a batch of new exploits and capabilities, a researcher said.
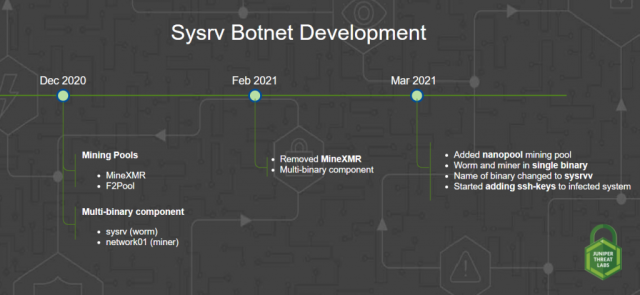
Research company Juniper started monitoring what it’s calling the Sysrv botnet in December. One of the botnet’s malware components was a worm that spread from one vulnerable device to another without requiring any user action. It did this by scanning the Internet for vulnerable devices and, when found, infecting them using a list of exploits that has increased over time.
The malware also included a cryptominer that uses infected devices to create the Monero digital currency. There was a separate binary file for each component.
Constantly growing arsenal
By March, Sysrv developers had redesigned the malware to combine the worm and miner into a single binary. They also gave the script that loads the malware the ability to add SSH keys, most likely as a way to make it better able to survive reboots and to have more sophisticated capabilities. The worm was exploiting six vulnerabilities in software and frameworks used in enterprises, including Mongo Express, XXL-Job, XML-RPC, Saltstack, ThinkPHP, and Drupal Ajax.
“Based on the binaries we have seen and the time when we have seen them, we found that the threat actor is constantly updating its exploit arsenal,” Juniper researcher Paul Kimayong said in a Thursday blog post.
Juniper Research
Thursday’s post listed more than a dozen exploits that are under attack by the malware. They are:
| Exploit | Software |
| CVE-2021-3129 | Laravel |
| CVE-2020-14882 | Oracle Weblogic |
| CVE-2019-3396 | Widget Connector macro in Atlassian Confluence Server |
| CVE-2019-10758 | Mongo Express |
| CVE-2019-0193 | Apache Solr |
| CVE-2017-9841 | PHPUnit |
| CVE-2017-12149 | Jboss Application Server |
| CVE-2017-11610 | Supervisor (XML-RPC) |
| Apache Hadoop Unauthenticated Command Execution via YARN ResourceManager (No CVE) | Apache Hadoop |
| Brute force Jenkins | Jenkins |
| Jupyter Notebook Command Execution (No CVE) | Jupyter Notebook Server |
| CVE-2019-7238 | Sonatype Nexus Repository Manager |
| Tomcat Manager Unauth Upload Command Execution (No CVE) | Tomcat Manager |
| WordPress Bruteforce | WordPress |
The exploits Juniper Research previously saw the malware using are:
- Mongo Express RCE (CVE-2019-10758)
- XXL-JOB Unauth RCE
- XML-RPC (CVE-2017-11610)
- CVE-2020-16846 (Saltstack RCE)
- ThinkPHP RCE
- CVE-2018-7600 (Drupal Ajax RCE)
Come on in, water’s great
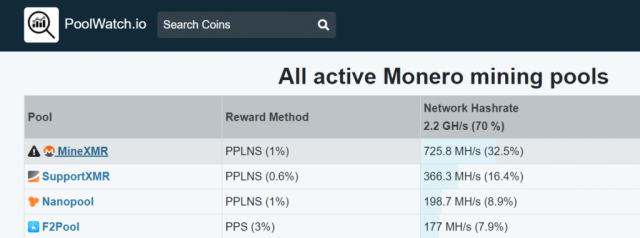
The developers have also changed the mining pools infected devices join. The miner is a version of the open source XMRig that currently mines for the following mining pools:
- Xmr-eu1.nanopool.org:14444
- f2pool.com:13531
- minexmr.com:5555
A mining pool is a group of cryptocurrency miners who combine their computational resources to reduce the volatility of their returns and increase the chances of finding a block of transactions. According to mining pool profitability comparison site PoolWatch.io, the pools used by Sysrv are three of the four top Monero mining pools.
“Combined together, they almost have 50% of the network hash rate,” Kimayong wrote. “The threat actor’s criteria appears to be top mining pools with high reward rates.”
Juniper Research
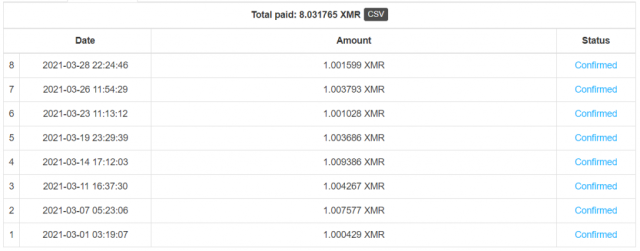
The profit from mining is deposited into the following wallet address:
49dnvYkWkZNPrDj3KF8fR1BHLBfiVArU6Hu61N9gtrZWgbRptntwht5JUrXX1ZeofwPwC6fXNxPZfGjNEChXttwWE3WGURa
Nanopool shows that the wallet gained 8 XMR, worth roughly $1,700 USD, from March 1 to March 28. It’s adding about 1 XMR every two days.
Juniper Research
A threat to Windows and Linux alike
The Sysrv binary is a 64-bit Go binary that’s packed with the open source UPX executable packer. There are versions for both Windows and Linux. Two Windows binaries chosen at random were detected by 33 and 48 of the top 70 malware protection services, according to VirusTotal. Two randomly picked Linux binaries had six and nine.
The threat from this botnet isn’t just the strain on computing resources and the non-trivial drain of electricity. Malware that has the ability to run a cryptominer almost certainly can also install ransomware and other malicious wares. Thursday’s blog post has dozens of indicators that administrators can use to see if the devices they manage are infected.
[ad_2]


